A lot can go wrong when validating SAML messages. When auditing SAML endpoints, it's important to look out for vulnerabilities in the signature validation logic. XML Signature Wrapping (XSW) against SAML is an attack where manipulated SAML message is submitted in an attempt to make the endpoint validate the signed parts of the message -- which were correctly validated -- while processing a different attacker-generated part of the message as a way to extract the authentication statements. Because the attacker can arbitrarily forge SAML assertions which are accepted as valid by the vulnerable endpoint, the impact can be severe. [1,2,3]
Testing for XSW vulnerabilities in SAML endpoints can be a tedious process, as the auditor needs to not only know the details of the various XSW techniques, but also must handle a multitude of repetitive copy-and-paste tasks and apply the appropriate encoding onto each message. The latest revision of the XSW-Attacker module in our BurpSuite extension EsPReSSo helps to make this testing process easier, and even comes with a semi-automated mode. Read on to learn more about the new release!
To simplify its use, the XSW-Attacker performs the attack in a two step process of initialization and execution, as reflected by its two tabs Init Attack and Execute Attack. The interface of the XSW-Attacker is depicted below.
The Init Attack tab displays the current SAML message. To execute a signature wrapping attack, a payload needs to be configured in a way that values of the originally signed message are replaced with values of the attacker's choice. To do this, enter the value of a text-node you wish to replace in the Current value text-field. Insert the replacement value in the text-field labeled New value and click the Add button. Multiple values can be provided; however, all of which must be child nodes of the signed element. Valid substitution pairs and the corresponding XPath selectors are displayed in the Modifications Table. To delete an entry from the table, select the entry and press `Del`, or use the right-click menu.
Next, click the Generate vectors button - this will prepare the payloads accordingly and brings the Execute Attack tab to the front of the screen.
At the top of the Execute Attack tab, select one of the pre-generated payloads. The structure of the selected vector is explained in a shorthand syntax in the text area below the selector.
The text-area labeled Attack vector is editable and can be used to manually fine-tune the chosen payload if necessary. The button Pretty print opens up a syntax-highlighted overview of the current vector.
To submit the manipulated SAML response, use Burp's Forward button (or Go, while in the Repeater).
First, open an intercepted request in Burp's Intruder (e.g., by pressing `Ctrl+i`). For the attack type, select Sniper. Open the Intruder's Positions tab, clear all payload positions but the value of the XML message (the `SAMLResponse` parameter, in our example). Note: the XSW-Attacker can only handle XML messages that contain exactly one XML Signature.
Next, switch to the Payloads tab and for the Payload Type, select Extension-generated. From the newly added Select generator drop-down menu, choose XSW Payloads, as depicted in the screenshot below.
While still in the Payloads tab, disable the URL-encoding checkbox in the Payload Encoding section, since Burp Intruder deals with the encoding automatically and should suffice for most cases.
Click the Start Attack button and a new window will pop up. This window is shown below and is similar to the XSW Attacker's Init Attack tab.
Configure the payload as explained in the section above. In addition, a schema analyzer can be selected and checkboxes at the bottom of the window allow the tester to choose a specific encoding. However, for most cases the detected presets should be correct.
Click the Start Attack button and the Intruder will start sending each of the pre-generated vectors to the configured endpoint. Note that this may result in a huge number of outgoing requests. To make it easier to recognize the successful Signature Wrapping attacks, it is recommended to use the Intruder's Grep-Match functionality. As an example, consider adding the replacement values from the Modifications Table as a Grep-Match rule in the Intruder's Options tab. By doing so, a successful attack vector will be marked with a checkmark in the results table, if the response includes any of the configure grep rules.
Our students Nurullah Erinola, Nils Engelberts and David Herring did a great job improving the execution of XSW and implementing a much better UI.
---
[1] On Breaking SAML - Be Whoever You Want to Be
[2] Your Software at My Service
[3] Security Analysis of XAdES Validation in the CEF Digital Signature Services (DSS)
[4] WS-Attacker
Testing for XSW vulnerabilities in SAML endpoints can be a tedious process, as the auditor needs to not only know the details of the various XSW techniques, but also must handle a multitude of repetitive copy-and-paste tasks and apply the appropriate encoding onto each message. The latest revision of the XSW-Attacker module in our BurpSuite extension EsPReSSo helps to make this testing process easier, and even comes with a semi-automated mode. Read on to learn more about the new release!
SAML XSW-Attacker
After a signed SAML message has been intercepted using the Burp Proxy and shown in EsPReSSO, you can open the XSW-Attacker by navigating to the SAML tab and then the Attacker tab. Select Signature Wrapping from the drop down menu, as shown in the screenshot below:To simplify its use, the XSW-Attacker performs the attack in a two step process of initialization and execution, as reflected by its two tabs Init Attack and Execute Attack. The interface of the XSW-Attacker is depicted below.
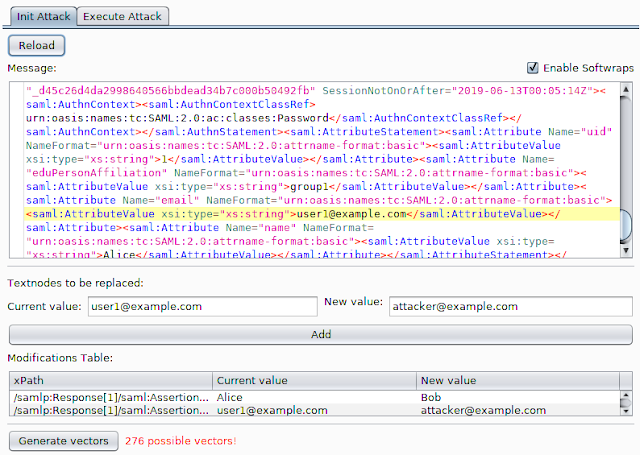 |
| XSW-Attacker overview |
The Init Attack tab displays the current SAML message. To execute a signature wrapping attack, a payload needs to be configured in a way that values of the originally signed message are replaced with values of the attacker's choice. To do this, enter the value of a text-node you wish to replace in the Current value text-field. Insert the replacement value in the text-field labeled New value and click the Add button. Multiple values can be provided; however, all of which must be child nodes of the signed element. Valid substitution pairs and the corresponding XPath selectors are displayed in the Modifications Table. To delete an entry from the table, select the entry and press `Del`, or use the right-click menu.
Next, click the Generate vectors button - this will prepare the payloads accordingly and brings the Execute Attack tab to the front of the screen.
At the top of the Execute Attack tab, select one of the pre-generated payloads. The structure of the selected vector is explained in a shorthand syntax in the text area below the selector.
The text-area labeled Attack vector is editable and can be used to manually fine-tune the chosen payload if necessary. The button Pretty print opens up a syntax-highlighted overview of the current vector.
To submit the manipulated SAML response, use Burp's Forward button (or Go, while in the Repeater).
Automating XSW-Attacker with Burp Intruder
Burp's Intruder tool allows the sending of automated requests with varying payloads to a test target and analyzes the responses. EsPReSSO now includes a Payload Generator called XSW Payloads to facilitate when testing the XML processing endpoints for XSW vulnerabilities. The following paragraphs explain how to use the automated XSW attacker with a SAML response.First, open an intercepted request in Burp's Intruder (e.g., by pressing `Ctrl+i`). For the attack type, select Sniper. Open the Intruder's Positions tab, clear all payload positions but the value of the XML message (the `SAMLResponse` parameter, in our example). Note: the XSW-Attacker can only handle XML messages that contain exactly one XML Signature.
Next, switch to the Payloads tab and for the Payload Type, select Extension-generated. From the newly added Select generator drop-down menu, choose XSW Payloads, as depicted in the screenshot below.
While still in the Payloads tab, disable the URL-encoding checkbox in the Payload Encoding section, since Burp Intruder deals with the encoding automatically and should suffice for most cases.
Click the Start Attack button and a new window will pop up. This window is shown below and is similar to the XSW Attacker's Init Attack tab.
Configure the payload as explained in the section above. In addition, a schema analyzer can be selected and checkboxes at the bottom of the window allow the tester to choose a specific encoding. However, for most cases the detected presets should be correct.
Click the Start Attack button and the Intruder will start sending each of the pre-generated vectors to the configured endpoint. Note that this may result in a huge number of outgoing requests. To make it easier to recognize the successful Signature Wrapping attacks, it is recommended to use the Intruder's Grep-Match functionality. As an example, consider adding the replacement values from the Modifications Table as a Grep-Match rule in the Intruder's Options tab. By doing so, a successful attack vector will be marked with a checkmark in the results table, if the response includes any of the configure grep rules.
Credits
EsPReSSO's XSW Attacker is based on the WS-Attacker [4] library by Christian Mainka and the original adoption for EsPReSSO has been implemented by Tim Günther.Our students Nurullah Erinola, Nils Engelberts and David Herring did a great job improving the execution of XSW and implementing a much better UI.
---
[1] On Breaking SAML - Be Whoever You Want to Be
[2] Your Software at My Service
[3] Security Analysis of XAdES Validation in the CEF Digital Signature Services (DSS)
[4] WS-Attacker
More articles
- Hack Tools Download
- Pentest Tools
- How To Make Hacking Tools
- Hacking Tools Pc
- How To Install Pentest Tools In Ubuntu
- Hacker Tools
- Pentest Recon Tools
- Hacker Hardware Tools
- Pentest Tools Download
- Kik Hack Tools
- Hack App
- Hacking Tools 2020
- Hack Tools For Games
- Hacker Tools For Pc
- Hacking Tools Download
- Tools Used For Hacking
- Hack Tools Mac
- Pentest Tools Review
- Hacking Tools Hardware
- Hacker Tools Windows
- Hacker Tools Linux
- Best Hacking Tools 2019
- Pentest Tools Framework
- Physical Pentest Tools
- Hacker Tools List
- Hak5 Tools
- Pentest Tools Github
- World No 1 Hacker Software
- Best Hacking Tools 2020
- Beginner Hacker Tools
- Hacking Apps
- Hacker Techniques Tools And Incident Handling
- Free Pentest Tools For Windows
- Pentest Tools Nmap
- Pentest Tools Url Fuzzer
- Hacking Tools For Kali Linux
- Pentest Automation Tools
- Best Hacking Tools 2020
- Hak5 Tools
- Hacking Tools For Windows Free Download
- Android Hack Tools Github
- Pentest Tools Download
- Pentest Automation Tools
- Nsa Hacker Tools
- Kik Hack Tools
- Hacking Tools 2020
- How To Install Pentest Tools In Ubuntu
- What Is Hacking Tools
- Hacking Tools Mac
- Tools For Hacker
- Pentest Tools Url Fuzzer
- Hacking Tools Download
- Hack Website Online Tool
- Hack Rom Tools
- Hacking Tools 2019
- Usb Pentest Tools
- New Hack Tools
- Physical Pentest Tools
- Pentest Tools For Mac
- Hacking Tools Windows
- Pentest Tools Framework
- Hacking Tools 2020
- Hacker Tools For Mac
- Pentest Automation Tools
- Hack App
- Hacker Tools Linux
- Top Pentest Tools
- Hacker Tools For Pc
- Hacking Tools Usb
- Hacking Tools For Kali Linux
- Best Hacking Tools 2020
- Hacking Tools For Windows
- Hack Tools For Ubuntu
- Pentest Tools
- Hacker Security Tools
- Hacker Tools
- Hacker Tool Kit
- Hacking Tools Software
- Beginner Hacker Tools
- Hack Tools Github
- Hacking Tools For Beginners
- Hacker Tools 2019
- Hacker Tools For Ios
- Hacking Tools For Games
- Hacker Tools
- Hacker Hardware Tools
- Pentest Tools Github
- Hacking Tools Github
- Tools For Hacker
- Hack Tools Github
- Ethical Hacker Tools
- Pentest Recon Tools
- Blackhat Hacker Tools
- Best Hacking Tools 2019
- Hacker Tools Online
- Hackers Toolbox
- Hack Tools Pc
- Hacker Tools 2020
- Hack Tools
- Hacking Tools For Pc
- Hacker Tools Linux
- Computer Hacker
- Hack And Tools
- Hack Tools Download
- Pentest Tools Alternative
- Computer Hacker
- Hack Rom Tools
- Hacker Tools 2020
- Hacking Tools Github
- Hacking Tools For Windows Free Download
- Hacker Tools 2019
- Best Pentesting Tools 2018
- Bluetooth Hacking Tools Kali
- Pentest Tools Nmap
- Hacker Search Tools
- Hacking Tools For Mac
- Pentest Tools Tcp Port Scanner
- Pentest Tools Website
- Pentest Tools Website
- Pentest Tools Apk
- Hacker Search Tools
- Hacker Techniques Tools And Incident Handling
- Hack Tools For Windows
- Best Hacking Tools 2020
- Free Pentest Tools For Windows
- Pentest Tools For Android
- Pentest Tools For Android
- Hacking Tools And Software
- Hacking Tools Github
- Computer Hacker
- Top Pentest Tools
- Pentest Tools For Ubuntu
- Hacking Tools Software
- Hacker Tools List
- Hack App
- Black Hat Hacker Tools
- Pentest Tools Port Scanner
- Pentest Tools Open Source
- Hack Tools
- Hack Tools For Mac
- How To Hack
- Hack Tools 2019
- Hacker Tools Online
- Hack Tools For Mac
- Hacker Hardware Tools
- Pentest Tools For Mac
- Hacks And Tools
- Underground Hacker Sites
- Hacking Tools For Windows Free Download
- Hack And Tools
- Hacking Tools Pc
- Hacking Tools Kit
- Pentest Tools Website
- Best Hacking Tools 2020
- Hacker Tools Free Download
- Pentest Automation Tools
- Hacking Tools Kit




Tidak ada komentar:
Posting Komentar